CMMC Insights Blog

CMMC Compliance
Microsoft GCC High and the 48 CFR Final Rule: Compliance Updates 2025
October 9th, 2025 by Matthew Locke
Learn how the 48 CFR Final Rule mandates Microsoft GCC High for DoD contractors handling CUI and key migration strategies for 2025 compliance.
CMMC Compliance
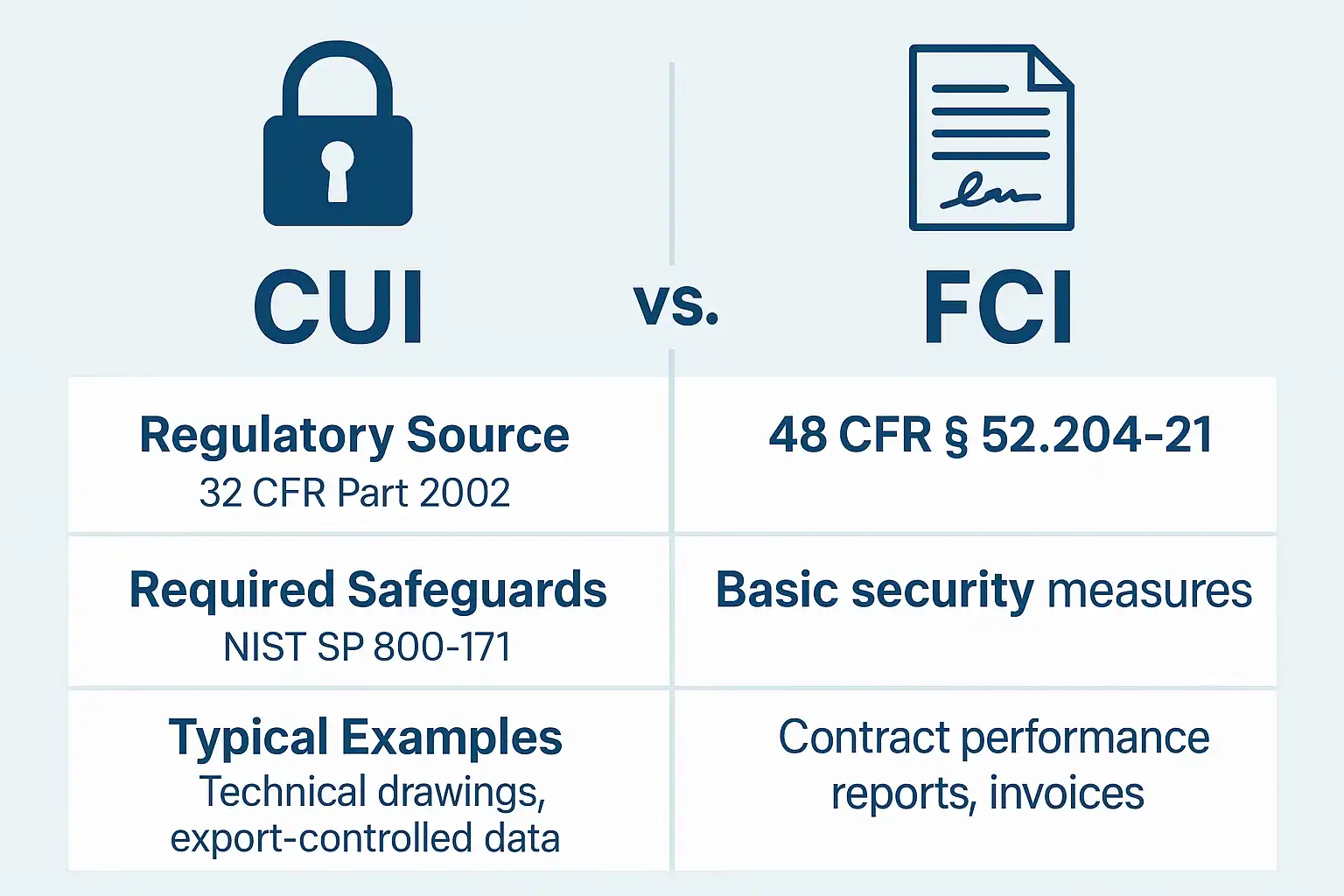
CUI vs FCI Under 48 CFR Final Rule: Defense Contractor Guide 2026
October 7th, 2025 by Jim Carlson
What's the difference between CUI and FCI under the 48 CFR Final Rule? A defense contractor guide to data classification and CMMC compliance in 2026.

CMMC Compliance
Anonymizing CUI for Subcontractors: CMMC Compliance Guide 2025
October 3rd, 2025 by Jim Carlson
Learn how to properly anonymize Controlled Unclassified Information (CUI) for subcontractors while maintaining CMMC Level 2 compliance and meeting DoD requirements.

CMMC Compliance
SIEM Requirements for CMMC Compliance in 2026
September 17th, 2025 by Matthew Locke
Does CMMC require a SIEM? Learn the NIST 800-171 logging and monitoring controls, what assessors actually look for, and practical SIEM alternatives for defense contractors in 2026.

CMMC Ruling
CMMC in Federal Acquisition: Understanding the Impact of the New 48 CFR Final Rule on Defense Contractors
September 11th, 2025 by Jim Carlson
See how the 48 CFR final rule makes CMMC mandatory for DoD contracts. Learn contractor obligations, recertification timelines, and compliance enforcement details.

CMMC Compliance
Microsoft 365 GCC High Migration: A CMMC Compliance Roadmap for Defense Contractors
September 4th, 2025 by Matthew Locke
Planning a GCC High migration? Learn tenant rebuild steps, PowerShell automation, CMMC Phase 2 requirements, and realistic costs for defense contractors in 2026.

CMMC Compliance
Is Vulnerability Data Controlled Unclassified Information? A Guide for Defense
September 3rd, 2025 by Matthew Locke
Find out when vulnerability data is classified as CUI and how defense contractors should secure it to meet CMMC and DoD cybersecurity compliance requirements.
CMMC Compliance
What Evidence is Needed for a CMMC Level 2 Assessment?
September 1st, 2025 by Matthew Locke
Learn what evidence is needed for CMMC Level 2 assessments, including policies, logs, configs, training records, and review proof to ensure compliance success.

CMMC Compliance
System and Communications Protection: Securing Data for CMMC Compliance
July 18th, 2025 by Jim Carlson
Learn how to secure your data in transit and at rest with System and Communications Protection practices essential for CMMC Levels 2 and 3 compliance.

CMMC Compliance
Securing Physical Access in CMMC: Mastering the Physical Protection Domain
July 11th, 2025 by Jim Carlson
Master the Physical Protection domain in CMMC by controlling facility access, using logs and badges, and applying compliance strategies for contractors.

Personnel Security
Personnel Security for CUI: Ensuring Trusted Access under CMMC
July 10th, 2025 by Jim Carlson
Learn how to implement Personnel Security controls to protect Controlled Unclassified Information (CUI) and meet CMMC Level 2 compliance requirements.

Cybersecurity
Incident Response Made Simple: Preparing for CMMC Compliance
May 30th, 2025 by Jim Carlson
Learn how to prepare and respond to cybersecurity incidents effectively to meet CMMC compliance with practical tips and tools for incident response readiness.

CMMC Compliance
Identification and Authentication in CMMC: How to Verify User Identities and Secure Access (Updated for Final 48 CFR Rule)
May 29th, 2025 by Jim Carlson
Learn the critical Identification and Authentication controls for CMMC Level 2 under the 48 CFR Final Rule. Implement MFA and account management with proper evidence for compliance.

Cybersecurity
Mastering Configuration Management in CMMC: How to Control Your System Settings and Changes Securely
May 20th, 2025 by Jim Carlson
Learn how to master Configuration Management in CMMC to control system changes securely and stay audit-ready. Key practices, tools, and compliance tips explained.

CMMC Compliance
Building a Security-Aware Workforce: Mastering the Awareness and Training Domain of CMMC 32 CFR Part 170
May 19th, 2025 by Jim Carlson
Master the Awareness and Training domain of CMMC 32 CFR Part 170 with tailored, ongoing cybersecurity education to protect your workforce and CUI.

CMMC Compliance
Mastering Audit and Accountability in CMMC: Essential Practices for Compliance
May 12th, 2025 by Jim Carlson
Learn how to master Audit and Accountability in CMMC Levels 2 and 3 with best practices, automation tips, and compliance strategies to protect your data.

CMMC Compliance
Understanding the Access Control Domain in CMMC: What You Need to Know
May 6th, 2025 by Jim Carlson
Learn about the Access Control domain in CMMC, its 14 essential practices, and how to ensure compliance with effective cybersecurity controls.

CMMC Assessments
Understanding the Role of CMMC Third-Party Assessment Organizations (C3PAOs) in Cybersecurity Compliance
March 26th, 2025 by Jim Carlson
Understand the critical role of C3PAOs in performing CMMC Level 2 assessments under the 48 CFR Final Rule and how they support DoD contractor certification.