CUI vs FCI Under 48 CFR Final Rule: Defense Contractor Guide 2026
Key Takeaways
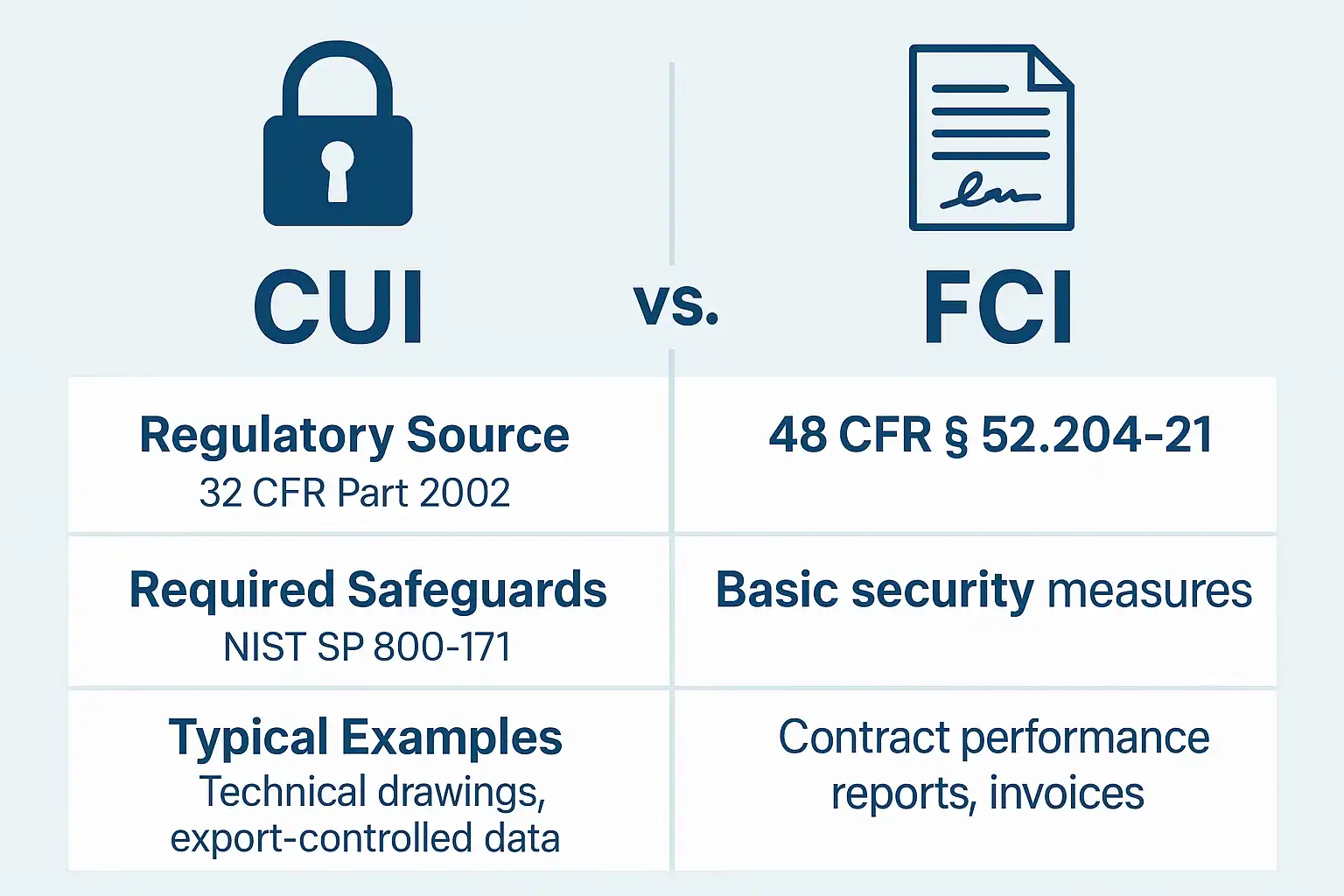
CUI (Controlled Unclassified Information) and FCI (Federal Contract Information) differ fundamentally in sensitivity and legal requirements, impacting cybersecurity controls and contract eligibility.
The 48 CFR Final Rule clarifies classification boundaries, documentation expectations, and flow-down obligations to subcontractors.
Accurate CMMC data classification is critical to avoid compliance failures and avoidable costs. With CMMC Phase 2 enforcement beginning November 10, 2026, contractors must get classification right now.
Introduction: The Final Rule Has Redrawn the Lines
TL;DR: The finalized 48 Code of Federal Regulations (CFR) rule settles long-standing confusion between CUI and FCI. For defense contractors navigating CMMC 2.0 requirements, distinguishing these categories is not just academic — it dictates how you plan and prove your cybersecurity defenses.
In our work helping defense contractors prepare for CMMC Level 2, we consistently see data classification as the number one stumbling block. Teams that get classification wrong end up either over-investing in controls they do not need or, worse, under-protecting data that requires full NIST 800-171 safeguards.
Understanding whether your data qualifies as CUI or FCI shapes your System Security Plan (SSP), controls implementation, audit readiness, and ultimately your contract eligibility. Misclassification risks compliance violations and lost business opportunities.
This guide provides an updated overview grounded in the 48 CFR Final Rule, the NARA CUI Registry, DFARS clauses, and the CMMC framework, giving contractors of all sizes the clarity to manage and document data classification confidently.
How Does the 48 CFR Final Rule Define CUI and FCI?
CUI is information that federal law, regulation, or government-wide policy requires safeguarding. FCI is information provided by or generated for the government under a contract that is not intended for public release. The distinction matters because each category triggers a different set of cybersecurity controls.
CUI (Controlled Unclassified Information) | FCI (Federal Contract Information) | |
|---|---|---|
| : Definition | CUI (Controlled Unclassified Information): Information the government creates or possesses that a law, regulation, or government-wide policy requires safeguarding | FCI (Federal Contract Information): Information not intended for public release, provided by or generated for the government under a contract |
| : Legal basis | CUI (Controlled Unclassified Information): NARA CUI Registry categories; laws such as ITAR, Export Control Act, Privacy Act | FCI (Federal Contract Information): FAR 52.204-21 contractual clause |
| : CMMC level required | CUI (Controlled Unclassified Information): Level 2 (110 controls per NIST SP 800-171 Rev 3) | FCI (Federal Contract Information): Level 1 (17 controls per FAR 52.204-21) |
| : Controls framework | CUI (Controlled Unclassified Information): NIST SP 800-171 Rev 2 (all 110 practices) | FCI (Federal Contract Information): FAR 52.204-21 (15 basic safeguarding requirements) |
| : Marking requirements | CUI (Controlled Unclassified Information): Must be marked per CUI category (e.g., CUI//DEFENSE//EXPORT) | FCI (Federal Contract Information): No formal CUI marking; protected from public disclosure under contract terms |
| : Subcontractor flow-down | CUI (Controlled Unclassified Information): Full NIST 800-171 implementation required | FCI (Federal Contract Information): FAR 52.204-21 compliance required |
| : Example data types | CUI (Controlled Unclassified Information): Vulnerability scans, technical drawings, ITAR-controlled specs, system architecture docs | FCI (Federal Contract Information): Contract schedules, timekeeping data, pricing proposals, internal comms tied to contract performance |
| : Assessment type | CUI (Controlled Unclassified Information): Third-party C3PAO assessment (Level 2) | FCI (Federal Contract Information): Self-assessment (Level 1) |
Note: NIST SP 800-171 Revision 3 was published in May 2024. CMMC Level 2 assessments currently use the Revision 2 control set, but DoD is expected to transition to Revision 3 in a future rule update. Contractors should monitor official CMMC announcements for the adoption timeline.
Which CMMC Level Do You Need for CUI vs FCI?
If your contract involves CUI, you need CMMC Level 2. If it involves only FCI, you need Level 1. The Cybersecurity Maturity Model Certification (CMMC) program ties data classification directly to required cybersecurity controls:
Level 1 (Foundational): Protects FCI exclusively, applying 17 controls from FAR 52.204-21. Verified by annual self-assessment.
Level 2 (Advanced): Applies to environments handling CUI and any associated FCI, requiring all 110 controls in NIST SP 800-171 Rev 3. Verified by third-party C3PAO assessment for critical programs.
Level 3 (Expert): Intended for specialized programs handling the most sensitive CUI, adding selected controls from NIST SP 800-172. Assessed by DCMA DIBCAC.
Mislabeling data may lead to either insufficient protection (if CUI is mistaken for FCI) or unnecessary expenditure (if all data is treated as CUI). Correct classification ensures compliance scope matches actual risk and contract requirements.
For a deeper look at how the 14 CMMC domains map to these levels, see our knowledge base.
Not sure whether your contracts involve CUI or FCI?
CMMC Dashboard helps you track your NIST 800-171 controls and document your compliance status.
What the 48 CFR Final Rule Clarifies
Explicit Boundary: FCI is strictly defined as contract-generated or provided data; CUI includes data protected under laws such as ITAR, Export Control, and Privacy Act authorities.
Documentation: Contractors must record their classification rationale within the SSP or related artifacts. For audit readiness, incorporating detailed evidence and logs is critical, aligned with CMMC Level 2 assessment evidence expectations.
Assessment Expectations: CMMC assessors require traceability linking contract clauses, data categories, and classification labels. Using a POA&M template to track gaps can support this process.
Flow-Down Rules: Subcontractors handling CUI must fully implement NIST 800-171. Those dealing only with FCI follow FAR 52.204-21. For granular guidance on subcontractor protections, see our guide on anonymizing CUI for subcontractors.
Consistent Categories: The NARA CUI Registry was updated to reflect DoD's critical infrastructure, export control, defense technical data, and other categories.
Classification is no longer a theoretical exercise but a traceable, auditable process woven into compliance documentation.
What Are Real-World Examples of CUI vs FCI?
CUI Includes:
System penetration test results or vulnerability scans on DoD systems.
Technical drawings and CAD files based on government-furnished information.
System architecture documents or interface specifications.
Export-controlled information governed by ITAR or EAR regulations.
Network diagrams showing CUI data flows and security boundaries.
FCI Includes:
Contract schedules and project management data not publicly releasable.
Timekeeping, labor cost reports for billing purposes.
Confidential pricing and proposal documents submitted to the DoD.
Internal communications connected to contract performance, but not marked CUI.
Meeting notes from contract status calls that do not reference controlled technical data.
Edge Cases
Not all data falls neatly into one category. These are the situations where contractors most frequently misclassify:
Derived data: A summary report that draws from CUI source material (e.g., a briefing slide that references vulnerability scan findings) becomes CUI even if the summary itself was created internally. The derived work inherits the classification of the source.
Aggregated FCI: Individual pieces of FCI are low-sensitivity, but when combined they may reveal patterns about military operations or capability gaps. If an aggregation rises to a level where a government marking authority would classify it, treat it as CUI until clarified.
Emails and chat logs: An email thread that starts as FCI (contract scheduling) can become CUI the moment someone pastes a technical data point, test result, or controlled specification into the thread. The entire thread inherits the higher classification.
Publicly available data enhanced with government context: Raw data sourced from public information is not CUI. But if the government provides context — such as identifying which public components are used in a weapons system — the combined information may be classified as CUI under the defense technical data category.
Vendor proposals with technical approaches: A pricing proposal is typically FCI, but if the technical approach section describes controlled methods, algorithms, or system designs, that section may qualify as CUI.
When in doubt, check the specific DFARS 252.204-7012 clause in your contract and consult the NARA CUI Registry categories for your data type.
How Does Data Classification Map to CMMC Domains?
The classification of your data determines which CMMC domains and controls apply. Here is how CUI and FCI map to the most relevant CMMC domain families:
CMMC Domain | Applies to CUI (Level 2)? | Applies to FCI (Level 1)? | Key Controls |
|---|---|---|---|
| CMMC Domain: Access Control (AC) | Applies to CUI (Level 2)?: Yes — all 22 controls | Applies to FCI (Level 1)?: Yes — 4 controls (AC.L1-3.1.1, .2, .20, .22) | Key Controls: Limit system access, control remote access, manage CUI flow |
| CMMC Domain: Identification & Authentication (IA) | Applies to CUI (Level 2)?: Yes — all 11 controls | Applies to FCI (Level 1)?: Yes — 2 controls (IA.L1-3.5.1, .2) | Key Controls: MFA, password management, device authentication. See CMMC MFA and password requirements |
| CMMC Domain: Media Protection (MP) | Applies to CUI (Level 2)?: Yes — all 9 controls | Applies to FCI (Level 1)?: Yes — 1 control (MP.L1-3.8.3) | Key Controls: CUI marking, media sanitization, transport protection |
| CMMC Domain: Physical Protection (PE) | Applies to CUI (Level 2)?: Yes — all 6 controls | Applies to FCI (Level 1)?: Yes — 4 controls (PE.L1-3.10.1, .3, .4, .5) | Key Controls: Facility access, visitor logs, physical device protection |
| CMMC Domain: System & Communications Protection (SC) | Applies to CUI (Level 2)?: Yes — all 16 controls | Applies to FCI (Level 1)?: Yes — 2 controls (SC.L1-3.13.1, .5) | Key Controls: Boundary protection, CUI encryption at rest and in transit |
| CMMC Domain: Audit & Accountability (AU) | Applies to CUI (Level 2)?: Yes — all 9 controls | Applies to FCI (Level 1)?: No | Key Controls: Log management, event correlation, retention. See SIEM requirements for CMMC |
| CMMC Domain: Configuration Management (CM) | Applies to CUI (Level 2)?: Yes — all 9 controls | Applies to FCI (Level 1)?: No | Key Controls: Baseline configs, change control, least functionality |
| CMMC Domain: Incident Response (IR) | Applies to CUI (Level 2)?: Yes — all 3 controls | Applies to FCI (Level 1)?: No | Key Controls: Incident handling, reporting, testing |
| CMMC Domain: Risk Assessment (RA) | Applies to CUI (Level 2)?: Yes — all 3 controls | Applies to FCI (Level 1)?: No | Key Controls: Vulnerability scanning, risk assessments |
| CMMC Domain: Security Assessment (CA) | Applies to CUI (Level 2)?: Yes — all 4 controls | Applies to FCI (Level 1)?: No | Key Controls: Plan of action, system monitoring, security assessments |
Key takeaway: FCI contracts require only 17 controls across 6 domains. CUI contracts require all 110 controls across all 14 domains. The classification decision is not a labeling exercise — it determines the entire scope and cost of your compliance program.
How Should Contractors Classify CUI and FCI?
Identify and categorize data early. Review contract clauses, especially DFARS 252.204-7012, 7019, and 7020, for CUI applicability. Maintain a data inventory detailing sources and classification.
Label and store correctly. Label CUI clearly using standard markings (e.g.,
CUI//DEFENSE//EXPORT). Store it in environments compliant with NIST SP 800-171 Rev 3. Mark FCI as "For Official Use Only" or a similar designation within systems compliant with FAR 52.204-21.
Manage mixed data environments carefully. When CUI and FCI coexist, apply CUI-level controls to the entire system unless the data is isolated via logical segmentation. If your organization uses Google Workspace or Microsoft 365 GCC High, your cloud environment boundaries must align with your CUI data flows.
Document your classification rationale. Within your SSP, cite contract clauses, specify data categories, and explain classification decisions to facilitate assessor verification. Ensure inclusion of detailed evidence and documentation per CMMC Level 2 evidence requirements.
Review classification regularly. Update classifications when contracts change, new government data is received, or system boundaries shift. The Phase 2 enforcement deadline of November 10, 2026 makes this especially urgent for contractors who have not yet begun their CMMC assessment process.
What Are the Most Common CUI vs FCI Mistakes?
Treating all contract information as CUI without legal basis. This leads to over-scoping: applying 110 controls to data that only requires 17. The cost difference can be tens of thousands of dollars.
Overlooking derived data generated from CUI sources. If your team creates a presentation that references vulnerability scan results or technical specifications, that presentation inherits CUI classification.
Neglecting to update SSPs and classification data after reclassification events. Contracts change. New data arrives. System boundaries shift. Your classification must keep pace, and so must your documentation.
Assuming FCI is not subject to controls. FCI still demands foundational safeguards per FAR 52.204-21. Ignoring these 17 controls can result in a failed Level 1 self-assessment.
Failing to classify data at the point of receipt. When the government furnishes data or when your team first creates contract-related information, that is the moment to classify. Retroactive classification across months of accumulated files is far harder and more error-prone.
Conclusion
Misclassification stands as a leading cause of failed CMMC assessments. The 48 CFR Final Rule demands not only safeguarding the correct data but also proving classification accuracy with robust documentation.
A disciplined, transparent classification program — consistent with NARA, DFARS, and NIST guidance — is your strongest foundation for compliance and for trust with Department of Defense partners.
With CMMC Phase 2 enforcement set for November 10, 2026, the window to get classification right is closing. Contractors who act now will be positioned for assessment readiness. Those who delay risk scrambling under deadline pressure.
Frequently Asked Questions
Ready to simplify your CMMC compliance and classification process?
Sign up for the CMMC Dashboard to access tools that help you track your data classification, map controls, and prepare for assessment.
Frequently Asked Questions
Frequently Asked Questions
Q: Is vulnerability data CUI?
Yes. Vulnerability data tied to DoD systems, including scans and penetration tests, is considered CUI due to its sensitive nature and falls under the CUI defense category in the NARA Registry.
Q: Does timekeeping data qualify as FCI?
Yes. Contract labor and time reports are FCI; they must be protected from public disclosure under contractual terms but do not require the full 110 NIST 800-171 controls.
Q: Is data created about a DoD agency from public sources classified as CUI?
No. Data compiled solely from public information does not constitute CUI. However, if the government provides additional context that elevates the information's sensitivity, the combined data may qualify as CUI.
Q: Can FCI become CUI?
Yes. If FCI incorporates or derives from CUI (such as summaries containing controlled technical data), it assumes CUI classification. This is one of the most common edge cases contractors encounter.
Q: Do subcontractors have identical protection requirements for FCI and CUI?
No. Subcontractors protecting FCI must comply with FAR 52.204-21, corresponding to CMMC Level 1 (17 controls). Those handling CUI must meet full NIST 800-171 Rev 3 requirements for Level 2 (110 controls).
Q: What distinguishes CUI Basic from CUI Specified?
CUI Basic requires NIST SP 800-171 safeguards and general handling rules. CUI Specified is subject to additional dissemination and marking rules dictated by specific laws or regulations like ITAR or the Privacy Act. Check the NARA CUI Registry to determine which category applies to your data.
Q: What's the best way to document classification for assessments?
Include detailed data types, associated contract clauses, and classification rationale within your System Security Plan or data inventory to make your process transparent for assessors. A POA&M template can help track any classification-related gaps alongside your control implementation progress.
Sources: 48 CFR Final Rule (effective 2025), NARA CUI Registry, DFARS 252.204-7012, FAR 52.204-21, NIST SP 800-171 Rev 3, CMMC Model Version 2.0, 32 CFR Part 170.
Get clarity on your CMMC scope
Track your NIST 800-171 controls and document your compliance progress, free.